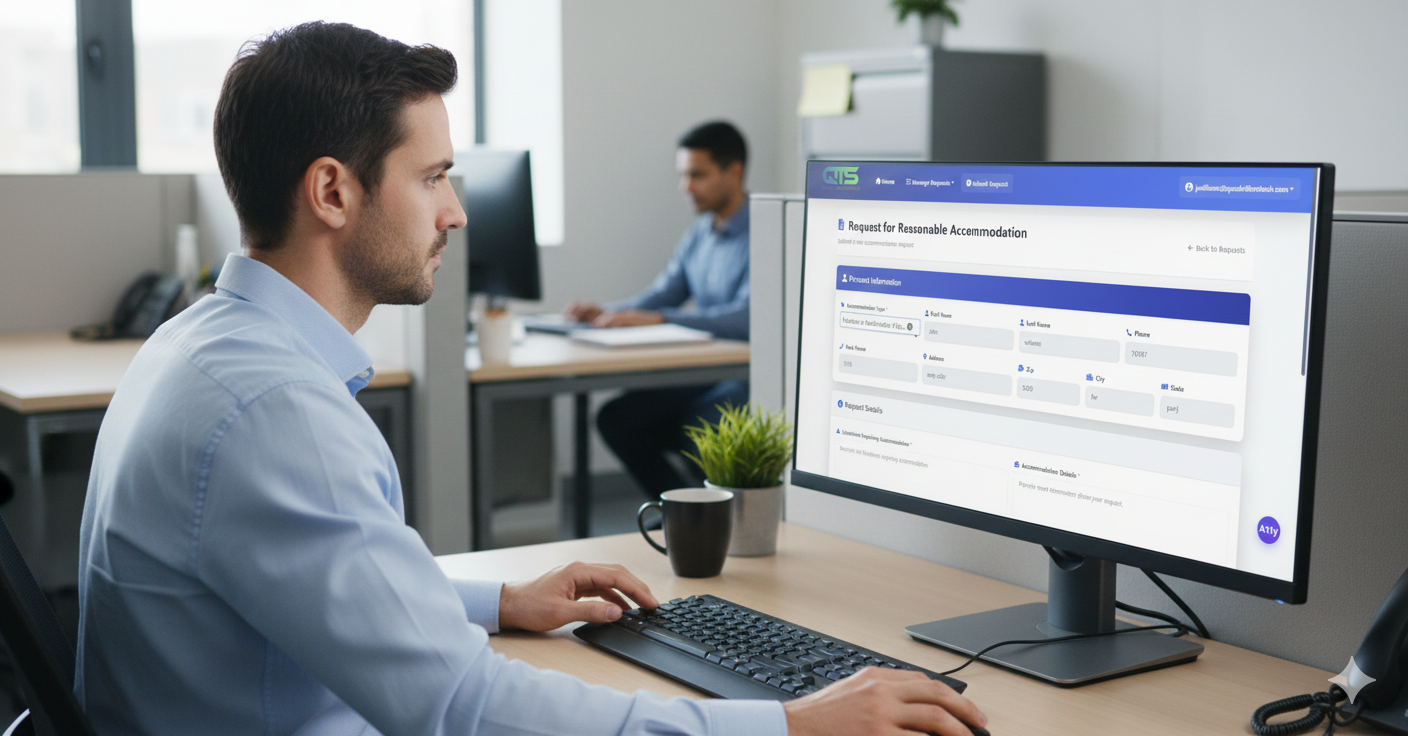
Built for Trust, Scale, and Workforce Protection
The Quadrillion Tech Reasonable Accommodation Tracking Platform is engineered for organizations of every size with security, reliability, and performance at the core. Our seasoned technology team safeguards sensitive workforce data with robust technical and administrative controls that protect information throughout its lifecycle.